Initial samples demonstrate that Magniber only targets Korean-speaking users and, if it does not detect Korean language on the infected system, it will terminate its processes and not encrypt any files. If it does detect the Korean language, it will search for files to encrypt and append either. Kgpvwnr, or.dxjay to the file names. If you need to decrypt versions 1, 4, 5.0.1 through 5.2, then download and run our new tool linked below. The wait is over. For victims of GandCrab versions 1, 4 or 5, there is a new decryption tool available from Bitdefender Labs to help you get your life and your data back – for free. How to remove Magniber virus and restore encrypted files. This article is dedicated to ransomware called Magniber which gets onto customers' machines around the world, and encrypts their files. Here we've assembled full info on Magniber's essence, and the deletion of Magniber from your system. Check out our video library AppCheck defending against newest ransomware, automatic recovery and real-time backup.
- Distribution Method : Automatic infection using exploit by visiting website
- MD5 : bdb30eefb423d7710d45501b2849bfad

- Major Detection Name :Trojan/Win32.Magniber.R216865 (AhnLab V3), Trojan.Win32.MyRansom.114880856 (ViRobot)
- Encrypted File Pattern : .ygshc
- Malicious File Creation Location :
- C:Users%UserName%AppDataLocalREAD_FOR_DECRYPT.txt
- C:Users%UserName%AppDataLocalygshc.exe
- C:Users%UserName%Desktop<Random>.exe
- C:WindowsSystem32Tasksygshc
- C:WindowsSystem32Tasks<Random>
- C:WindowsSystem32Tasks<Random>1
- Payment Instruction File : READ_ME_FOR_DECRYPT.txt
- Major Characteristics :
- Offline Encryption
- Only run on Korean operating system
- Change the default values of the registry entry 'HKEY_CLASSES_ROOTmscfileshellopencommand' and disable system restore (wmic shadowcopy delete) using Event Viewer (eventvwr.exe)
- Auto execute ransomware (pcalua.exe -a C:Users%UserName%AppDataLocalygshc.exe -c <Random>) and payment instrucition file (pcalua.exe -a notepad.exe -c %LocalAppData%READ_FOR_DECRYPT.txt) every 15 minutes by adding Task Scheduler entries
- Auto connect MY DECRYPTOR site (pcalua.exe -a http://<URL>) every a hour by adding Task Scheduler entries
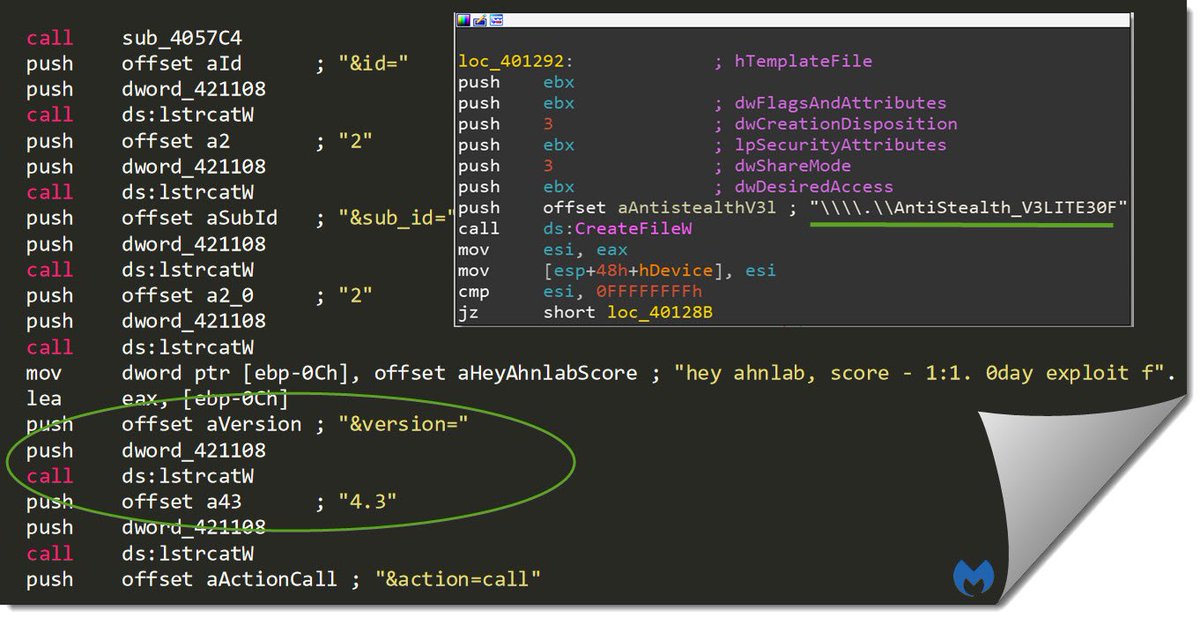
Magniber is a ransomware distributed by Magnitude's operator. The latest version of Magniber has been upgraded in a comprehensive way in terms of encryption method, infected object, etc. This article comprehensively analyzes the latest version of Magniber from the perspectives of its attack process, harm, behavior analysis, comparison with earlier version, security protection measures, etc. Magnitude EK is a long-lasting browser exploit tool that has been very active since its inception in 2013, and through which multiple ransomware packages have been distributed - from Cerber to Magniber, GangCrab, etc. The tool has been one of the favorite tools for ransomware users worldwide. Magniber is a ransomware distributed by Magnitude's operator. The original version of Magniber mainly targets South Korea and has a relatively simple encryption method. The latest version of Magniber has been upgraded in a comprehensive way, and can infect many Asian countries including China, and has a quite different encryption method. The latest version of Magniber exploits the CVE-2018-8174 VBScript engine memory corruption vulnerability of Internet Explorer (please refer to related article for vulnerability analysis). This article comprehensively analyzes the latest version of Magniber from the perspectives of its attack process, harm, behavior analysis, comparison with earlier version, security protection measures, etc. Magniber's attack process is mainly divided into the following stages: Magnigate’s 302 redirection A Base64 obfuscated JavaScript is used to launch Magnitude’s landing page A Base64 encoded VBScript is used, the main functionality of which is to determine whether the CVE-2018-8174 vulnerability exists. If the vulnerability exists, the shellcode is executed and the payload (the first dll) is downloaded The dll loader unpacks the Magniber’s core dll and injects it into a process The core dll completes the proceses of local file traversal and encryption for ransom Let's first take a look at Magniber's traffic view[1], as shown below: (The image is from Malwarebytes [1]) It can be found that after Magnigate's 302 redirection, the Base64 encoded and obfuscated JavaScript and VBScript are called. The original JavaScript is as follows: The decoded JavaScript is as follows: The decoded VBScript main function is as follows (for detailed information about VBScript, please refer to another article 'Microsoft VBScript Engine Remote Code Execution Vulnerability (CVE-2018-8174) Analysis Report'): As can be seen from the VBScript, the functionality implemented by the script is to judge whether the VBScript UAF vulnerability CVE-2018-8174 exists. If the vulnerability exists, the vulnerability is triggered and the type confusion is used to save and execute the constructed Shellcode by constructing the VirtualProtect structure. The shellcode executed is as follows: In terms of functionality, the Shellcode is a simple downloader which will download the obfuscated load dynamic link library (load.dll), decode it with the key through XOR operation, and deploy it. The downloaded load dynamic link library (load.dll) is still not the core of Magniber ransomware. The main functionality of load.dll is to load the next stage program, extract Magniber's core DLL (core.dll), and inject the core DLL into a process. Both DLLs, with Reflective Loader stub, load themselves into a current process using the Reflective DLL injection technique. For the Reflective DLL Injection technique, please refer to [2]. After the core DLL is loaded into the process, it will soon be found that files (including compressed files, Office documents, scripts, images, videos, etc.) in all directories will be encrypted and added with the extension .dyaaghemy, and a README.txt file (roughly means you need to pay a ransom to decrypt the files) will be placed in the current directory, as shown below: The link in the given README.txt points to an onion web interface that is unique to each victim and similar to many other ransomware pages: (The image is from malwarebytes[1]) Each file encrypted by the latest version of Magniber has a .dyaaghemy extension, and each file is encrypted with a unique key. The encrypted content is completely garbled, indicating that a stream cipher or a blockchain cipher (probably AES encryption in CBC mode) is adopted by the attacker. The effect of Magniber infection is as follows (take php file as an example): The latest version of the Magniber contains 2 dlls, of which 72fce87a9766a8c09ed844564adc75 is just the next stage loader that unpacks Magniber's core DLL (19599cad1bbca18ac6473e64710443b7) and injects it into a process. 4.1 Load dll (load.dll) Behavior AnalysisLoad.all code is relatively simple, and its main functionality can be understood through static analysis. The entry function of load.dll is as follows: After getting into the core processing function, we can see that it carries out a process injection, as shown below: Next, open the local notepad and write the data: Query current process information: Get the information about the module loaded by the current process: 4.2 Core dll (core.dll) Behavior Analysis4.2.1 Core.dll Overall Structure4.2.2 Core.dll Specific AnalysisCore.dll Entry: Follow up the execfunc() function. If there is a function pointer in the corresponding position, execute: Follow up the sub_10008768 function to get into the core processing function main(). It first judges the system language, if not Chinese (Hong Kong), Chinese (Macau), Chinese (Simplified), Chinese (Singapore), Chinese (Taiwan), Korean (Korean), Malay (Malaysia), it directly call the function 1000 to exit. Please refer to the link [3] for specific language ID. Then a series of operations on the memory layout are carried out, the result is as follows: Next, the advapi32.dll is loaded to clear the memory area, extend the environment variable string, and replace the environment variable string % PUBLIC% with the current user-defined value: Next, call the 4FA8 function to create the mutex dyaaghemy (the extension of the encrypted files): Call GetTickCount to get 19 random strings: Copy the URL and other information to get the disk drive letter: Get disk information: Encrypt the primary and logical disks: Call 59F7 in 64C4, compare it with the folder under the C drive, and encrypt the disk files: Traverse the file, determine whether the file is an executable file and other attribute values, and obtain a random value to prepare for the encryption operation: Use the encryption function provided by the system to generate the encryption key: File encryption: Generate ransom information: Then operate the registry and execute other commands: After all the work is completed, a data pack is sent to report completion: For analysis of earlier version, please refer to link [4]. Compared with the earlier version, the new version mainly has the following changes: (1) A lot of code obfuscation techniques are adopted Compared with previous version of Magniber, a lot of effort has been put into code obfuscation, and the code is obfuscated via a variety of different techniques. First of all, API functions are now dynamically retrieved by their checksums: Dynamic retrieval: a function pointer is obtained by searching the export table of the currently loaded dll. In addition, some of the parameters for the calls are dynamically calculated and junk code is added in between the operations. A string that is supposed to be loaded is scattered through several variables: (2)More countries are targeted The previous version of Magniber only targets South Korea, the new version of Magniber is aimed at more countries. The supported languages are Chinese (Simplified, Taiwan, Singapore), Korean (Korean), Malay (Malaysia), etc. (3) File encryption File encryption of the earlier version depends on the AES key downloaded from the CnC server (if not available, it returns to a hard-coded key, in which case file encryption is relatively easy). This time, Magniber comes with a public RSA key of the attackers that makes it fully independent from the Internet connection during the encryption process. This key is used for protecting the unique AES keys used to encrypt files.
1. The spread of Magniber is mainly based on the Internet Explorer's latest VBScript engine memory corruption vulnerability, namely CVE-2018-8174. Therefore, you first need to fix the vulnerability to avoid the harm of the ransomware. Fix suggestions: fix the vulnerability CVE-2018-8174 according to the vendor-provided patch: https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-8174[9]. 2. Deploy an IPS product to block related attacks. HUAWEI has released a signature database to detect CVE-2018-8174, please upgrade to the latest version which can be downloaded at https://isecurity.huawei.com/sec/web/freesignature.do Reference Links [1]https://blog.malwarebytes.com/threat-analysis/2018/07/magniber-ransomware-improves-expands-within-asia/ [2]https://github.com/stephenfewer/ReflectiveDLLInjection [3]https://www.cnblogs.com/wangweixf/archive/2008/08/15/1268537.html [4]https://blog.malwarebytes.com/threat-analysis/2017/10/magniber-ransomware-exclusively-for-south-koreans/ [5]http://wubingdu.cn/download/ReimageRepair [6]http://wubingdu.cn/download/mb3-setup [7]http://asec.ahnlab.com/1124 [8]https://gist.github.com/evilsocket/b89df665e6d52446e3e353fc1cc44711 [9]https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-8174 1.Magniber(load.dll): 6e57159209611f2531104449f4bb86a7621fb9fbc2e90add2ecdfbe293aa9dfc 2.Magniber(core.dll): fb6c80ae783c1881487f2376f5cace7532c5eadfc170b39e06e17492652581c2 3.Javascript: https://gist.github.com/malwarezone/62e765a5d238360af68c9ca654cc4513#file-3-vb 4.VBScript: https://gist.github.com/malwarezone/62e765a5d238360af68c9ca654cc4513#file-4-vb |

Ahnlab Magniber Decrypt V4
Ahnlab Magniber Decrypt V4.1
157****7036 2019-01-29 20:10:44 dsd